Equifax Security Breach: How to Check & Fix (If Necessary)
AL
Last updated 10/31/2022 by
Andrew LathamEquifax announced in 2017 that criminals gained “unauthorized access” to the personal data of 143 million U.S. consumers and an undisclosed number of UK and Canadian residents.
143 million
Number of U.S. consumers affected by the security breach
Update: FTC settlement
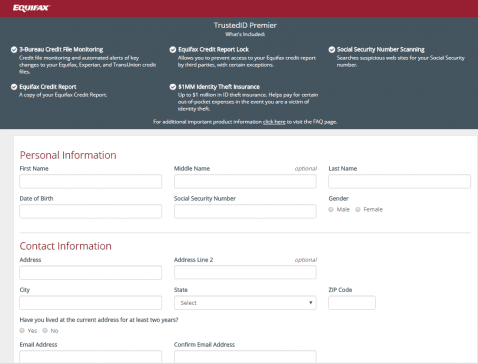
The Federal Trade Commission announced a settlement with Equifax that includes $425 million for the 147 million people who had their data compromised (source). If your information was exposed (check here), you can file a claim for your piece of the settlement here. You can choose between 10 years of free credit reporting or $125 in cash. You can also claim up to $20,000 for expenses caused by the breach, such as unauthorized charges caused by identity theft and the cost of freezing your accounts. Don’t forget to include the time you spent dealing with the breach. You can claim up to $25 an hour. And you don’t have to offer documentation to support your claim if it’s for 10 hours or less of your time. Here is a step-by-step guide to checking whether you were impacted by Equifax’s security breach. Equifax is offering one year of free credit monitoring with TrustedID Premier but the enrollment period ends in November. This service includes $1 million in identity theft insurance. You may have heard that accepting the free credit monitoring and identity theft includes an arbitration clause in the terms of service that would, in theory, waive some of your legal rights related to a class action. However, Equifax representatives have stated the class action waiver applies to the free credit monitoring and identity theft protection products, not the cybersecurity incident (source). New York Attorney General Eric Schneiderman has already stated publicly that this language is unenforceable. 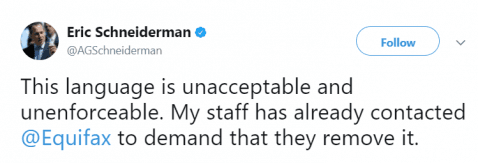
Compare Credit Report Services
Compare multiple vetted providers. Discover your best option.
How can I check whether my personal information was compromised in Equifax’s cybersecurity incident?
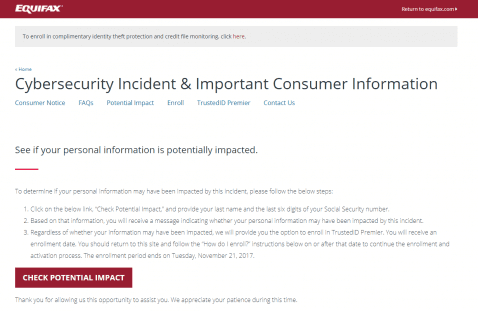
Equifax has set up a website to let consumers know whether their data was accessed by criminals. The website is a little clunky to use so here’s a short guide.
- Visit Equifax’s secure incident site . This is an official site that is linked to from Equifax’s press release on the breach.
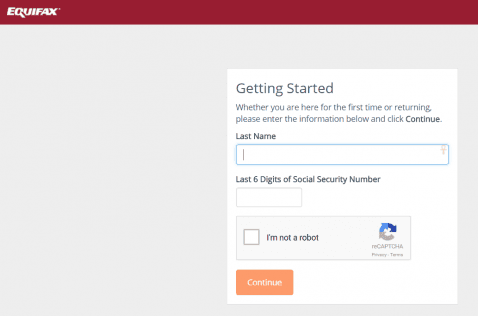
 2. Provide your last name and the last 6 digits of your SSN.
2. Provide your last name and the last 6 digits of your SSN.
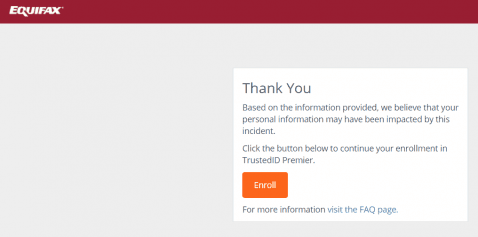
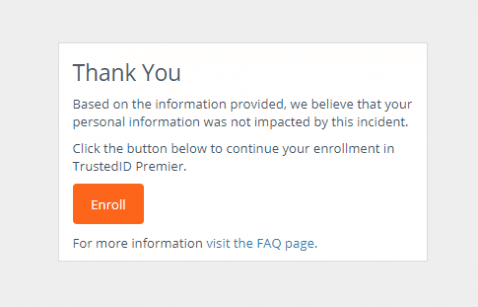
 3. See if you were affected and register with TrustedID Premier. Even if you haven’t been affected you can still get free credit reporting. Notice that you don’t get a clear message if your information is safe. Only consumers whose data was stolen receive a clear message.
3. See if you were affected and register with TrustedID Premier. Even if you haven’t been affected you can still get free credit reporting. Notice that you don’t get a clear message if your information is safe. Only consumers whose data was stolen receive a clear message.
 4. Check your credit reports from all three bureaus (Equifax, Experian, and TransUnion) regularly. Credit Sesame also offers free credit reporting.
4. Check your credit reports from all three bureaus (Equifax, Experian, and TransUnion) regularly. Credit Sesame also offers free credit reporting.
 5. See whether you have an email or a username that has been compromised in a data breach. This website is a good place to start.
5. See whether you have an email or a username that has been compromised in a data breach. This website is a good place to start.
What should you do next?
The Federal Trade Commission recommends taking the following steps if you suspect your personal information was compromised:
- Take advantage of free credit monitoring (see above for instructions on how to get free enrollment with TrustedID Premier). You can also get free credit reporting from Credit Sesame. Remember you will be giving up the right to sue Equifax in a class action.
- Access your credit reports and check any charges or accounts you don’t recognize.
- Contact your bank or credit card to cancel your credit card (if your credit card number was compromised).
- Consider a credit freeze on your credit accounts. A credit freeze makes it harder for criminals to apply for a new account in your name. If you don’t place a credit freeze, you may want to at least place a fraud alert. To place a credit freeze or fraud alert, call one of the credit bureaus and report you were the victim (or potential victim) of identity theft. Ask them to confirm they will also contact the other two bureaus.
These are the numbers and links to set up a credit freeze with the three national credit bureaus.
- Equifax — 1-800-349-9960
- Experian — 1‑888‑397‑3742
- TransUnion — 1-888-909-8872
5. Change any passwords and usernames (if possible) that may have been impacted by the breach. 6. Check any financial sites you’re registered with for unauthorized charges or transactions.
Is the information provided in Equifax’s “check your potential threat” website meaningful?
It is hard to say whether Equifax’s “check potential impact” website is accurate and reliable. At this stage, only Equifax knows what data has been affected. As several have noted, you get a ” your information may have been affected” message if you input Test and 123456, which does seem sloppy. However, we also got a “we believe your personal data was not affected” when we using Xyz, Thisisatest, Trump, and 123456. 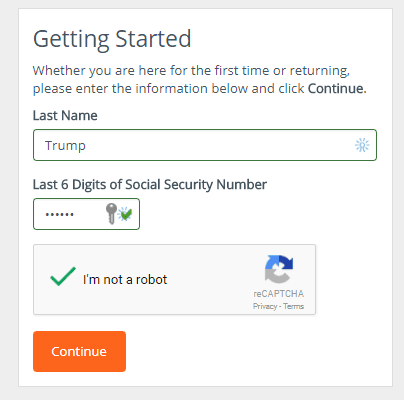
What information did the hackers access from Equifax’s databases?
Hackers obtained the names, Social Security numbers, birth dates, addresses and, in some instances, driver’s license numbers of approximately 143 million consumers. So pretty much all the information you don’t want in the hands of criminals. The credit card numbers and dispute documents of 209,000 “lucky” customers were also accessed.
How did the hackers steal the data?
Criminal hackers exploited a vulnerability in one of Equifax’s U.S. websites to access consumers’ files for three months (May to July 2017). Apparently, Equifax was hacked because they did not make a simple security update to one of their web applications, Apache Struts. As it happens, the only thing standing in the way of 143m people getting their identity jacked was Equifax’s failure to make a simple security update with one of their web applications, Apache Struts. A vulnerability that has existed and been known for nine years. Ouch. To make things even worse, it turns out Equifax was notified about the issues two months before the breach.
This is clearly a disappointing event for our company and one that strikes at the heart of who we are and what we do. I apologize to consumers and our business customers for the concern and frustration this causes”Richard F. Smith, chairman and chief executive of Equifax
While investigating the breach, Equifax realized information on Canadian and UK residents was also compromised. “This is clearly a disappointing event for our company and one that strikes at the heart of who we are and what we do. I apologize to consumers and our business customers for the concern and frustration this causes,” said Richard F. Smith, chairman and chief executive of Equifax in a statement published on the company’s website.
Equifax security breach is a PR nightmare
What could be worse for a credit reporting bureau than having to admit a security breach that affects millions of consumers? How about the fact three senior executives dumped almost $1.8 million in Equifax stock in the days after the company discovered the security breach (source). Sadly, this is not the first time Equifax’s data has been breached. Last year, identity thieves stole the tax and salary data from Equifax’s W2Express site. W2Express is a site that makes electronic W-2 forms accessible for download for many large companies, such as Kroger (source). Kroger, which employs more than 431,000 people, stated the following in a letter to all its employees: “It appears that unknown individuals have accessed [Equifax’s] W2Express website using default log-in information based on Social Security numbers (SSN) and dates of birth, which we believe were obtained from some other source, such as a prior data breach at other institutions”. The data obtained in this breach could also be used to obtain access to similar sites that require personal information, such as your SSN and date of birth. Protect yourself from these breaches by learning how hackers use your personal information and regularly checking your credit reports.
AL
Andrew is the Content Director for SuperMoney, a Certified Financial Planner®, and a Certified Personal Finance Counselor. He loves to geek out on financial data and translate it into actionable insights everyone can understand. His work is often cited by major publications and institutions, such as Forbes, U.S. News, Fox Business, SFGate, Realtor, Deloitte, and Business Insider.
Share this post: