Former Anonymous Superhacker Talks Fintech Cyber Security
S
Last updated 03/19/2024 by
SuperMoneyHector Xavier Monsegur also known also by the online pseudonym Sabu, is an American computer hacker known for being part of a small, ultra-skilled group of hackers within Anonymous and co-founder of the hacking group LulzSec. The groups claimed responsiblity for cyber attacks against government systems in Tunisia, Algeria, as well as the U.S. Senate, corporations such as Sony Corp, PBS, and Newscorp, as well as security firms like HBGary and Mantech – to name a few.
SuperMoney Founder, Miron Lulic caught up with Hector to uenderstand his perspective on cyber security and how Fintech startups can improve their security measures in today’s world. Here are prominent parts of the interview, where Hector talks about everything from how users can protect their identity online to how startups can reinforce their security systems. Read on.
Get Competing Personal Loan Offers In Minutes
Compare rates from multiple vetted lenders. Discover your lowest eligible rate.
It's quick, free and won’t hurt your credit score
Can you provide a brief bio about yourself and your experience within the cyber security space?
These days I’m an advisor and Lead of Penetration Testing for Rhino Security Labs, located out in Seattle, Washington.
In a previous life, I was convicted of hacking in 2011. I was able to reform and change my life around for the best. This situation, and turning over a new leaf has presented me with wonderful opportunities to not only give back to the community but help my customers with their concerns.
What are some common misconceptions about financial cyber security?
One of the biggest misconceptions many financial institutions have yet to deal with is equating compliancy with being secure. From a legal standpoint, compliancy may be the difference between having a security compromise written off or having a compromise be the end of the institution.
Security incidents in organizations like J.P.Morgan and others prove this notion. I feel very strongly about taking security seriously and approaching it from several angles:
a) Education
b) Pre-emptive security measures
c) Pro-active security measures
In hindsight, this can be applied to any organization or business although when it comes to financial cyber security, there are various steps an organization must take to ensure that sensitive customer information is properly safeguarded from would-be attackers. From the end-users’ perspective, it gets a bit complicated and much more difficult. The end-user, very much like an employee at a financial institution, is the weakest link to any secure environment. They face an almost infinite attack surface: phishing (email, VOIP), malware (drive-by, or targeted), security vulnerabilities (0-day, 1-day) and a plethora of other vectors. I believe that the aforementioned (education, pre-emptive and pro-active) measures would help and would deter most attacks, but there is almost no guarantee against dedicated attacks.
Thus, security awareness becomes part of one’s lifestyle as opposed to an add-on.
Are there any common financial cyber security mistakes you see a lot, and how can they be avoided?
Password re-use has been a major problem for internet users going back to the beginning. With the rise of large-scale compromises, large amounts of passwords are stolen and users face the risk of compromise on third-party sites. It is common practice, especially these days, for attackers to go through lists of dumped passwords and associated email addresses, and ironing out which accounts work on what sites.
This can be problematic, especially if a user re-uses their password across all of their financial accounts.
What are some ways one can protect themselves from financial related fraud online?
There are many ways the average person can protect themselves from compromise, many of which are not difficult to implement.
Generate unique and high entropy passwords per account, preferably with the use of a strong password manager.
Password managers like KeePass will generate strong entropy passwords, or allow you customize password generation. It is also a great organization tool for your credentials, and sensitive information.
Enabling 2FA or similar post-authentication security features on your accounts. 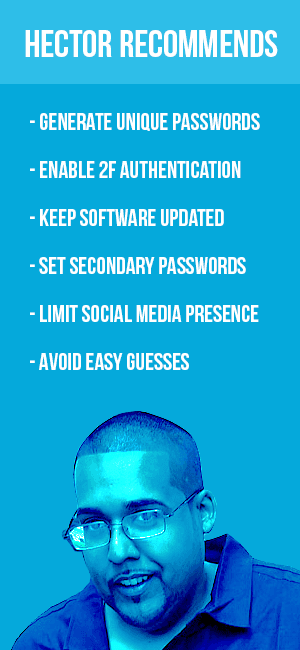
These come in various flavors and have their pros and cons respectfully. In most cases, the company hosting your account will provide their own technology. The most common is 2FA (via SMS, Email or Phone call).
Being mindful of the software you run, and keeping them up to date is very important.
This applies to everything from software, your operating system, and your phones and tablets.
Set secondary passwords with cellular, banking and healthcare providers.
It is not unheard of for someone to wake up in the morning to find their cellphones have been deactivated, and transferred to another sim. By setting a secondary password with your mobile provider, you’re limiting the attack scope from social engineers who call into technical support pretending to be you.
Limit, minimize or be very aware of your social media presence, including having a grasp of the kind of personal information is out there.
This allows you to minimize your attack surface, but also have an idea of what kind of attacks can be employed against you.
Avoid using easily guessable security questions, answers and the classic “mothers maiden name.”
Attackers have an assortment of tools and information, allowing them to guess a portion of your questions and answers.
With the venture capital world flocking to fund fintech startups, what are your thoughts on the capability of these startups to securely protect this intimate data from hackers?
Startups have a lot on their plate, and if they do not include a strong security policy into their infrastructure from the beginning of their formation, it becomes a major problem down the road. With the many obstacles startups face on a day to day operation, it’s very easy for them to put security on the backend especially if they have to deliver for investors in a timely fashion.
I’ve seen a split in startups over my time working with them. In many cases, I’ve seen daunting cases of lax of security measures. However, almost equally I’ve seen very good practice and security implementation from developers to at least safeguard applications against common risks. Let us hope that the latter becomes more prevalent.
What can startups entering the fintech space do to protect their user data?
Be careful how you place user data on the internet, but more specifically on cloud providers. Relying on a third parties security is a major problem.
Understand their attack surface.A lot of startups entering the fintech space are reliant on compliance and at most vulnerability assessment. There is more to securing user data than that, and I believe that understanding what you have and what attackers may want is a good step forward.
Next step is to be careful how you place user data on the internet, but more specifically on cloud providers. Even if a company maintains a strong security policy, having lapse security configurations in cloud services like AWS would allow an attacker to simply walk in and exfiltrate sensitive information.
Relying on a third parties security is a major problem, and there should be more thought and planning involved in this process.
I’ve seen lots of startups indicate that user data is safe because they use ‘bank-level’ encryption. What does this mean and should a user be satisfied?
Secondly, the technology commonly used to power HTTPS, which is the OpenSSL library, has had a lot of security problems since inception. Between downgrade attacks, to weaker cryptographic algorithms to replay attacks – users find themselves at the mercy of Man-in-The-Middle scenarios.
Just because it looks like your data is flowing to its intended target does not mean it is. It also does not mean that once your data reaches its intended target, that the servers are securing your data properly.
What should users look for to better judge level of security of a financial institution claiming “bank-level security”?
Users should use due diligence in looking over the security history of the institution they are going to do business with. Do they have financial stability? If not, how are you sure they’re able to 1) Pay developers to emphasize proper security practice, but 2) Are they able to repay you in case the worst occurs?
Do they have a history of security compromise? What’s the context behind those compromises?
Does the company force your web requests through HTTPS, and is there a lock beside the URL in the URI bar? When you click on the lock, does it provide you valid information about the company?
Are there reviews online about how the company operates? If the company is compromised, who regulates them? Are they a legal entity?
There are many questions, and fortunately, the answers are Google queries away.
Citibank experienced a major security breach several years ago. In your opinion, is consumer data safe with large established financial institutions?
There is no such thing as a 100% secure environment. The bigger the company, the broader the attack surface.
Absolutely not. The bigger the company, the broader the attack surface. Even if the financial institution has their own security teams, do monthly security audits with various security companies, make use of the bug bounty system, and are compliant – there is no guarantee that the institution can safeguard your information.
There is no such thing as a 100% secure environment. Always keep in mind that your personal information is one compromise away from happening.
This is fact and is not meant to scare you. My point here is to make you aware of the possibility that a compromise can occur and its better to be:
1) Educated about the possibility
2) Be pro-active about your personal security
3) And be pre-emptive. Have an emergency plan in case something like a major compromise occurs.
What reforms do you feel are necessary to improve the overall banking/financial system?
I’m no legal expert here, so I don’t think I can provide a real answer. Some ideas, however:
– I believe there should be tougher consequences for financial institution who do not invest or push strong security practice
– Fines and lawsuits make corporations change bad practice. Consumers should be made aware of their options and should be given support
Where do you see personal finance cyber security headed in the next few years?
I think a strong trend will be the removal of passwords at some point, making authorization or authentication a much more personal affair. This would require that mobile devices, gadgets like yubikeys, or other mediums are thoroughly tested and properly audited and finessed before something like this makes sense.
As more users become more security conscience, and companies are forced to take security and encryption a bit more seriously is when we will see serious change. There is little regulation, or consequence, for lax security practices.
There are compliance regulations in place, but companies who face a realistic consequence for user data compromise or breaches seem too low to make a difference. Attorney Generals need to be more involved in the process, or a regulatory system of overseers involved to make sure financial institutions are on top of their security practices.
Share this post: